There have long been rumors in the InfoSec community that in the wake of recent revelations, foreign institutions embraced old school means of keeping their secrets safe. Namely, once again embracing the typewriter.
Where the fear of an insider turning over hard copy secrets to outsiders once drove institutions to embrace electronic means, with all their corresponding safeguards, now it is electronic communications and cyberspace overall that are considered the primary threat. The increasing hostility of cyberspace has tainted the once-steady process of technological adoption for the time being.
It seems turning back the clock is a natural reaction for recent victims of cyberattacks. A shopping trip to a renowned supplier of luxury clothes and shoes, recently the victim of a large breach resulting in attackers potentially walking away with 1.1 million customer credit card numbers, introduced us to a similar security posture. We were informed that the chain had once again embraced the carbon-copy credit card machines as a means of processing purchases.
A quick visit to the surrounding luxury boutiques revealed a similar threat posture, with some store clerks visibly proud at the ingenuity of their brands in mitigating the highly-publicized threat.
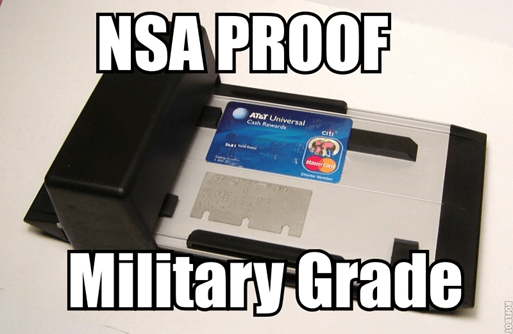
At a time of increasing uncertainty, insecurity, and hostility, the quickly expanding market for ‘NSA-proof’, ‘military-grade’ solutions should remember that while a superficial assessment of the field looks ripe for marketing big-ticket, all-in-one security solutions, vendors are more likely to embrace the tried-and-true old school methods and forego untested innovation altogether.
We’d do well to understand their viewpoint. The threats of cyberspace are very real and involve crippling costs. Prominent examples abound as multiple incidents involving POS malware have generated immense buzz of late. It turns out that many of these big-name cases involve the same malware (or a closely related variant) -as in the case of Home Depot, presumably attacked by the same BlackPOS malware as Target late last year. Similarly, Dairy Queen has been hit with Backoff, which has been used in more than one instance, thus proving that nothing is holy to cybercriminals, not even the home of the beloved blizzard.
This buzz has not escaped security experts and businesses alike, as both are eager to unearth greater information regarding these attacks and the vulnerable state of point-of-sale security. For those interested in countering the Backoff malware (and don’t much fancy the notion of readopting archaic credit card machines), I refer you to my colleagues’ analysis of the Backoff command and control servers.
Returning to typewriters can be considered a solution to our modern problems only if we forget some of the reasons we left typewriters behind in the first place. The old nightmare of an insider turning over hard copy secrets to outsiders is back (not that it ever went away). And even if you trust each and every one of your employees with your life, we mustn’t forget all that can be accomplished by the charm of the adept social engineer.
Using obsolete technologies for the sake of security is like betting on horse carriages at the dawn of the auto industry. Sure, they’ll get you places but they sure as hell won’t beat a car. Businesses don’t need to forego the benefits of modern technologies and interconnection that have allowed them to flourish in the dawn of the 21st century. Early cars were once unsafe and unreliable and thoughtful adaptation matured them into the secure and indispensable staples of modern life they are now. We are witnessing the growing pains of cyberspace -with proper tools, self-assessment, and sober reinforcement by layers, we may just see it into adulthood.
 data breach
data breach


 Tips
Tips