The current surge in remote working has raised cybercriminal interest in Office 365, one of the most common cloud collaboration platforms.
The basic scheme is simple: Cybercriminals lure a company employee to a fake Office 365 login page and persuade them to enter credentials. In other words, it is phishing. The specific methods by which the attackers try to get usernames and passwords differ, but here are the most common tricks of the trade.
Fake Teams messages
As a rule, when attackers send an e-mail message meant to look like a Microsoft Teams notification, they stress urgency, hoping the recipient won’t take a minute to note any irregularities. So, the general thrust may be something about an urgent deadline, for example, leading the victim to click the Reply in Teams button and end up on a fake login page.
If the attackers did their homework, the name and picture of a real colleague will be in the notification, which might look something like an internal BEC, but more commonly, it will be some abstract person. The cybercriminals’ calculation is also that the victim’s anxiety about someone unfamiliar having such an urgent matter will force a click on the button.
Delivery failure notification
Another fake problem crafted to instill a sense of urgency in the recipient is an alleged delivery failure, for example due to an authentication error. In this case, the victim was meant to click through to pick up a message, but the attackers were lazy and failed to create a plausible Office 365 login page.
Of course, next time they might make a more convincing fake, in which case the recipient would have to fall back on other means of identifying phishing. It’s worth noting that senders, not recipients, get delivery failure notices — if the server were able to identify the intended recipient, then it would deliver the message properly!
Full mailbox notification
Warning a victim of dire consequences — in this case, the horrible prospect of an undelivered message — the full mailbox notification is simply another aspect of herding workers into a panicked error. The choice it presents is to delete or to download the messages. Most people will opt for the latter and click the bait, a “Click here” button.
Note that in this case the attackers made some effort, inserting a paragraph in the е-mail about the company’s social responsibility in light of the pandemic, although they didn’t bother with even minimally convincing business English. Again, reacting out of panic can cause people to overlook the signs of a fraudulent communication.
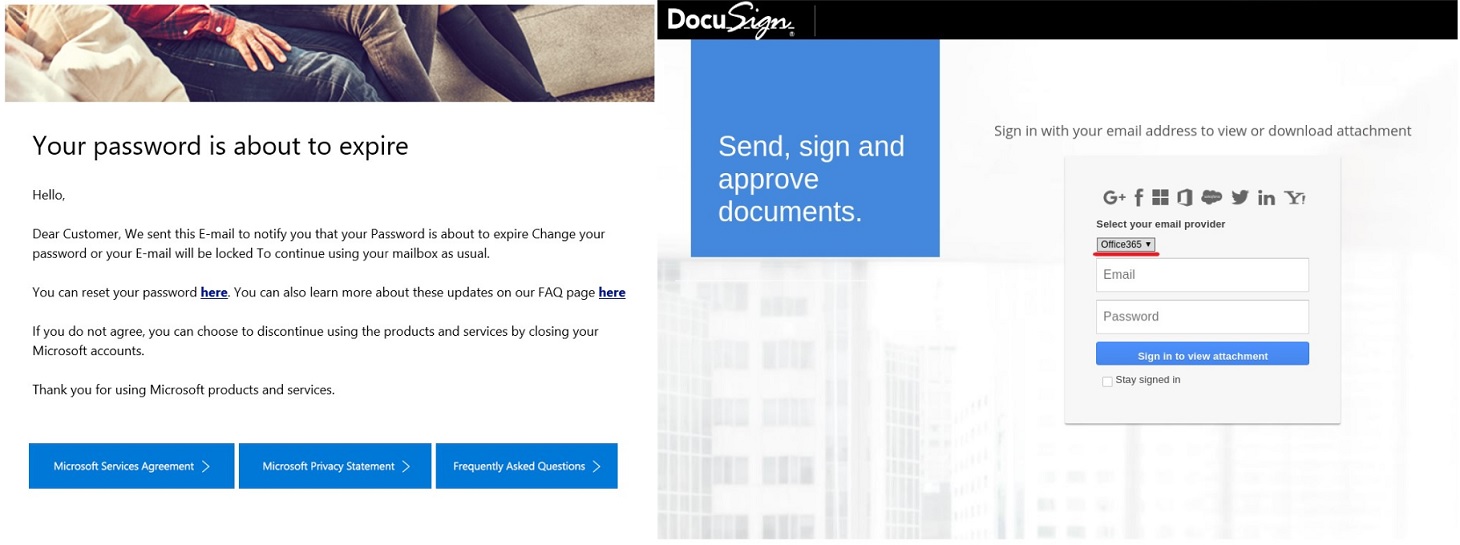
Password expiry notification
Changing a password is a fairly common procedure. Your company policy should require it regularly, and security may request it as a precaution against a possible leak. And, of course, when you set a new password, you have to provide the old one. Therefore, password-change requests are a staple of phishing е-mails.
Even if you somehow miss the sloppy language in the е-mail, the login page doesn’t stand up to scrutiny.
How to avoid getting hooked
Remember that account details unlock not only the ability to send е-mails from an employee’s address, but also access to all information accumulated in the mailbox. Any page requesting work account credentials deserves scrutiny, even if —especially if — you’re experiencing pressure to get things done fast. Two essential pieces of advice are all you need, here:
- Always check the address of any page asking for credentials. Depending on the service, legitimate login pages might include microsoftonline.com, outlook.office.com, onmicrosoft.com, or your company domain name.
- Deploy a robust security solution company-wide that blocks such phishing е-mails.
 phishing
phishing




 Tips
Tips