Apple in Disgrace
In late February, researchers detected a couple of major problems with the operating systems Apple iOS and Mac OS X.
The iOS version 7.06 update restored some certificate-validation checks when establishing a secure connection, and Secure Transport failed to validate the authenticity of the connection. In other words, an attacker with a privileged position on the victim’s network would be able to capture or modify data in sessions protected by SSL/TLS. And if you used a public wireless network, like in a cafe or an airport, to access online banking, Gmail or even Facebook a skilled attacker on the same network could wiretap the data transmitted by your device. At the same time, Safari would confirm that the session was protected with encryption, saying it was secure.
The same vulnerability was found in Mac OS X and patched pretty quickly. The cause of the bug appeared to be a simple programmer’s error – a duplicated line of code.
However, after one serious vulnerability had been eliminated another flaw was detected, which was hardly any less serious. The critical bug allowed some applications to monitor and record all user touch/press events on the smartphone’s screen and buttons. This bug is particularly dangerous because the vulnerability could be exploited by a specially designed application and already installed programs without the need to jailbreak the device.
Having two vulnerabilities come to the forefront in such a short period of time is not just worrisome, but almost disgraceful for those who still consider Apple’s operating systems to be fully protected against information threats. The system administrators in companies with adopted BYOD paradigms should pay closer attention to Apple products even though most threats have traditionally been posed to other platforms up until now.
It should also be noted that in the middle of March, there was a report about the iOS 7.1 update detailing the fixing of as many as twenty flaws. The conclusions here are pretty apparent.
The obscure 100 Gb/s
The Californian web-hosting company, Namecheap, experienced an extremely powerful DDoS-attack, exceeding 100 Gb/s at its peak. The company announced that it was “a new type of attack” that they had never faced before.
Namecheap is a large company with more than 800,000 clients throughout the world. Its DNS infrastructure encompasses three continents, so they are quite accustomed to DDoS attacks. However, this attack in particular was much more upsetting. We are talking about a new type of attack after all.
Namecheap’s spokespersons were unclear in defining whether this attack was generally unknown up until that point, or if it was just Namecheap that hadn’t dealt with something like that before.
We have recently heard a lot about DDoS attacks exploiting vulnerable NTP servers to enhance trash traffic. According to the DDoS mitigation specialists at Prolexic, high-bandwidth NTP amplification DDoS attacks are up 371.43 percent in the last 30 days.
The intensity of this type of attack can achieve significantly higher rates than the one that Namecheap had to tackle.
Unfortunately, the abundance of vulnerable NTP servers that are more prone to being used as DDoS tools really calls for a fresh assessment of the threat of DDoS-attacks in general. Namecheap is going to “improve and greatly expand DNS infrastructure as well as build up capacity to absorb and block hostile traffic,” even though this time around they managed to repel the attack in a few hours.
Will hosting companies with the less ambitious and powerful infrastructures be able cope with this type a problem though?
The threat Landscape is changing constantly: more and more often we can see unexpected targets for cyber attacks and our perception of what is secure and what is not is also changing.
The over-the-air backdoor
A conspiracy scandal erupted in mid-March around Galaxy branded devices, which appeared to have a backdoor that could give an attacker “over-the-air remote control” access to a phone’s file system, turning it into a spying tool.
Developers behind the Replicant project, a Cyanogen-based Android OS, initially discovered the backdoor was included in “most proprietary Android systems” running on Galaxy devices. The Galaxy Nexus S, S, S2, Note, Nexus, both the seven-inch and 10.1-inch Tab 2 and the Note 2 are all affected by the backdoor, according to Replicant.
Technically speaking, the problem rests in a program, Android’s Radio Interface Layer (RIL), which runs on the devices’ baseband processor that is in charge of handling the communication with the modem. That program, Samsung’s IPC protocol, allows the modem to “perform remote file I/O operations on the file system” via a class of requests called RFS commands. The program affords the user the ability to read, write and delete files on the phone’s storage.
It is totally unclear how that backdoor got into the operating system, it is likely to have been used by developers for some entirely legitimate purposes, because they are so obviously titled (IPC_RFS_READ_FILE, IPC_RFS_WRITE_FILE, IPC_RFS_RENAME_FILE, etc.). Maybe they just forgot to shut the backdoor afterwards. But we should all keep in mind the fact that this is not the first time Samsung devices have had weird bugs, including those capable of reading data and changing the settings unbeknownst to users. This may just imply that the presence of these devices within a corporate network can pose a threat to sensitive data if the system administrators have not taken proper care to protect mechanisms, like access rights to the data for different devices and users.
A Trojan racehorse
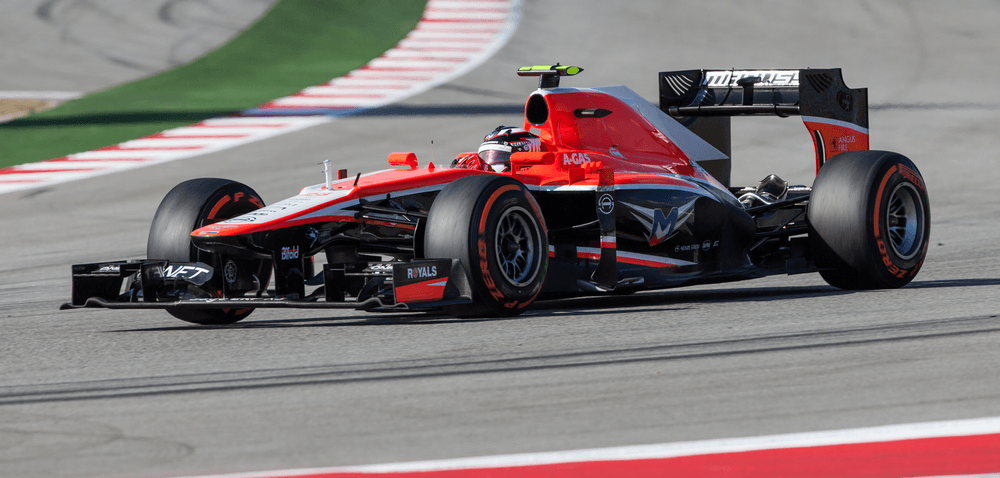
The Anglo-Russian Formula One racing team Marussia F1 encountered an unexpected problem- a Trojan in its computer systems, which greatly affected the whole team’s preparations for the coming race.
Just like conventional vehicles, modern racing cars are crammed with electronics. In order to effectively monitor and control all of the systems, racing teams use whole datacenters in miniature.
Imagine a Trojan getting into such a system. The team had to spend almost the whole day uprooting it and losing precious time. In four days before the test runs in Bahrain, the Marussia’s car could only do 29 laps – less than all the other teams.
In this case the Trojan did not attack the car’s onboard systems, but its external monitoring systems did suffer.
However, the safety systems of vehicles (primarily civilian) have worried experts with questions and concerns in the past.
Last year two experts showed how to disable the brakes, along with other systems, of Ford Escape smart cars. Although it required a physical connection to the automotive system (a connected laptop), even earlier in 2010 other researchers had demonstrated the possibility to remotely execute code in the onboard vehicle system via a wireless network.
Most cases of hacking onboard systems were for academic experiments conducted by experts from various organizations and universities. In particular, representatives of the University of South Carolina and Rutgers University showed how to hack into a system for the purposes of monitoring tire pressure. In turn, experts from the University of Washington and the University of San Diego wrote a program that allowed you (when connected directly to the onboard computers) to turn off the brakes and block the engine.
But there was at least one case of malicious activity when a former car sales center employee in Austin, Texas, gained control of the network system of remotely locking cars (they fired the employee, but forgot to reset the password). Eventually, more than a hundred drivers could not start their cars or have them stop signaling.
There is clearly enough evidence to suggest automotive systems are vulnerable to external influences. It’s not too difficult to then imagine the serious consequences successful hacking could entail.
Running fire at Linux
The Experts of ESET company announced in mid-March that they were able to identify a large scale malicious campaign, in which attackers hacked servers running Linux, FreeBSD and other Unix-related operating systems. The resulting botnet was used for spamming up to 35 million messages per day.
Within a timespan of two years, the attackers behind Operation Windigo infected more than 25,000 servers with malware, 10,000 of which are still under their control. The hackers also hold 700 compromised web servers, which are regularly used to steal SSH data and redirect up to 500,000 people every day to sites with malicious content.
Apparently there were seasoned professionals involved who really knew the features of the operating systems and were able to very effectively disguise any of their activities. The cross-platform malicious code that they created was quite secret, too. It left almost no trace on hard drives, so it was very difficult to detect. Removing it completely from the system was also very hard. The technical details are available here.
Why were Linux servers compromised? The attackers apparently followed a series of quite fair assumptions. Firstly, Linux is extremely popular in the server area. Secondly, the servers lend significant computing power by default and, more importantly, they provide broadband channels. Thirdly, Linux has the reputation of a protected operating system. As you can see, the technical savviness of the intruders proved sufficient enough to take advantage of the weaknesses of the server software, secretly taking over control of a large number of servers and receiving seemingly decent money from it.
If this is true, you cannot be sure someone else won’t repeat this attack, perhaps with even greater success.
Conclusion
Make no mistake in saying the overall threat landscape is changing. We often see seemingly unexpected targets become the victims of attacks, breaking our notion of what is protected and what is not. Since the beginning of the year, multiple vulnerabilities in Apple software have been revealed. Fortunately, there are no real cases of exploitation (or at least there is no information about such incidents). But servers under Linux and varieties of BSD endured very serious probing, and keep in mind the fact that they are still considered to be very hackerproof.
We have also seen the increasing popularity of the new type of DDoS attacks that use NTP amplification. The method itself is not new, but attackers have found it quite handy recently to the chagrin of victims.
A key recommendation for businesses in this regard is to keep track of new trends in the field of information threats. Even if up until now defense against cybercriminals has been twofold, divided amongst businesses and individual users, companies need to become active participants in the confrontation of risks. Defensive measures are now necessary, if not just for the fact that the use of vulnerable, unpatched server software poses a risk not just to individuals, but also to business infrastructures as a whole.
 security news
security news


 Tips
Tips