Cybersecurity experts have a problem. Actually, they have lots of them, but there is one particularly persistent and unsettling. It had to be approached with a worldwide operation, but seemed to have only temporary results.
So, what’s the thing?
- Subject: Gameover ZeuS
- Type: Highly resilient P2P botnet
- Malicious agent: Banking Trojan
- Additional threats: Cryptolocker Ransomware (distribution)
- Estimated size: 350,000 – 1 million PCs (globally)
- Status: Dismantled, C&C servers down (temporarily?)
- Status of Owner(s): Indicted, in hiding
- Forecast: Reactivation in a few weeks
Okay, it is dismantled. A fabulous Operation Tovar took place earlier this year, a joint effort between a multitude of international law enforcement agencies and security vendors from around the globe. Together they took on the botnet and managed to bring down its C&C servers.
But ultimately none had claimed the victory won: announcing that the botnet’s command servers are down, international police forces and security vendors also said that the users affected by the botnet had as little as two weeks to clean up their computers and to get rid of the botnet’s agent. Experts anticipate that Gameover ZeuS owners will soon launch new C&C servers, effectively restoring the botnet at least partially.
Vast in scope, Operation Tovar has only temporarily disrupted Gameover ZeuS.
Tweet
Gameover ZeuS has been around for three years now, but it’s fair to say that it actually has a longer history because its malware agent is based partially on the code of the original ZeuS Trojan, first detected in 2007. This code “leaked” in 2011, and it didn’t take long for cybercriminals to build numerous derivatives. Gameover is one of them, but its “toxicity” proved to be just way above the average.
ZeuS variants have been used for stealing banking credentials and financial fraud; Gameover Zeus’ owners went further, presumably using the botnet in high-dollar corporate account “takeovers”, with massive DDoS attacks used as a smokescreen.
Worse even: apparently Gameover ZeuS owners loaned parts of their network to the third parties, which used it to spread one of the most hated malware in recent times – Cryptolocker Trojan/ransomware, a machine of mass-extortion.
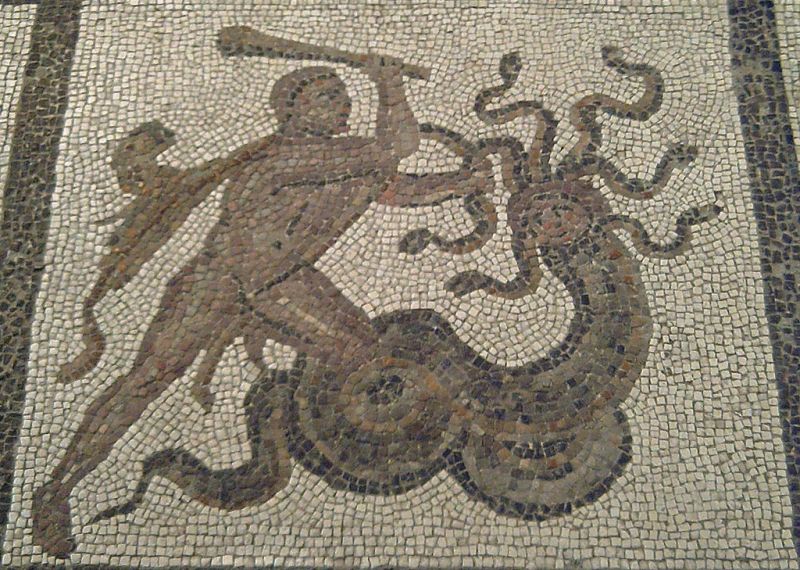
In early June 2014 the U.S. Department of Justice announced that so-called Operation Tovar (“Tovar” means “a commodity, ware” in Russian), had temporarily succeeded in cutting communication between Gameover ZeuS and its command-and-control servers. It proved to be rather difficult, much more than dismantling a common botnet, since Gameover uses an advanced peer-to-peer approach (or mechanism) to control and update the bot-infected systems. This makes it similar to mythical Hydra: many heads instead of the one, and even if the collective “Hercules” lops some of them off, it won’t take long before new heads are there.
Later the name of the main suspect – a presumed owner of botnet – had been announced: Evgeniy Mikhailovich Bogachev, a 30-year-old Russian national. US authorities pressed federal indictment charges against him. Experts, however, believe that the botnet is controlled by a few people, not just one Bogachev.
There is little doubt that the Gameover ZeuS will be back soon. It is hurt and inactive now, but definitely not dead. Why? Because, first, there are still up to a million infected boxes across the world. Some users may have received notifications from their ISP, some users are still clueless that their PCs are infected. So unless there is a global and extremely thorough clean-up campaign launched right now, the basis of the botnet will stay almost intact.
And even if it shrinks, repopulating it would be, most likely, fairly easy: Gameover had been disseminated via the notorious Cutwail botnet, which is still alive despite all attempts to bring it down. Why not using it again?
Owners of Gameover ZeuS are still at large. Indictment is in place, but it doesn’t mean that the person in question will be apprehended any time soon and it doesn’t mean that this is “the right guy”: any person is innocent until proved otherwise in court. In a nutshell, the botnet owner(s) is (are) free and sound, and most likely in a mood to regain their source of illicit income.
And, after all, there are source codes of ZeuS all over the cyber underground, changing hands and getting upgraded (or spoiled). So this story will go on and on.
Now, what is it to be done? It would be a dream come true if security vendors and law enforcement agencies would promote some sort of a Global Cyber Clean-Up Day, to take place, say, on August 31, so that both common users and businesses of all sizes, take one day to check their PCs with all possible tools and eradicate all threats.
A global home users cyber clean-up campaign would be fantastic. Is it just a fantasy?
Tweet
But then again, it’s rather a dream. Botnets mostly consist of old, underwatched Windows XP boxes with free or long-expired antivirus, and they stay that way for as long as they can be booted at all. There’s litle hope that their owners would pay attention to such campaign.
So for now, users and businesses should take care of themselves and their infrastructure, using “traditional” means: antimalware solutions (by the way, Kaspersky Lab’s products detect and block both ZeuS, Gameover ZeuS and Cryptolocker, no matter all their nastiness). Electronic payment protection should also be at place to make sure your money won’t go in an unexpected direction.
And staying sharp is a good idea, too.
P.s. It is also relevant to cite earlier recommendations from our Senior Security Researcher David Emm how to stay safe from Cryptolocker and Gameover:
“To keep your financial information safe (from Zeus, and from other malware designed to steal your money), just follow these simple rules:
- Don’t click on links you receive from unknown senders (by emails or in social media networks).
- Don’t download, open and keep unknown files on your device.
- Don’t use open unsecured (public) Wi-Fi networks for any transactions. Use openVPN traffic encryption.
- Always double-check the webpage before entering any of your credentials or confidential information – phishing sites are deliberately designed to look authentic.
- Work only with websites with the ‘https’ prefix; they are more secure than those with ‘http’.
- Make sure you have up-to-date anti-malware protection installed.
- If you don’t currently have any Security Software installed you can download it from our online store.
Don’t forget to use the same protection when using your mobile/tablet device for any transactions”.
 botnets
botnets