Kaspersky Lab has just publicized the discovery of a new cyber-espionage campaign. Unlike previous threats, it’s targeting smaller entities – namely SMBs. That’s where it gets interesting.
Grabit and run
Grabit is a rather fresh campaign: the data gathered so far indicates it launched some time in late February 2015. As almost half of the total number of infections (44.87%) occurred in Thailand (with India as a distant second – 24.36% and US as an even more distant third – 10.26%), it could have been a local operation. Still, the first samples arrived to Kaspersky Lab’s experts from the company’s partners in USA.
Grabit gets distributed via a Microsoft Office Word (.doc) email attachment containing a malicious macro AutoOpen.
#Grabit – an #SMB-targeting spy campaign. #Protectmybiz
Tweet
The following is a quote from Securelist’s thorough (as usual) analysis of the malware:
“This macro simply opens a socket over TCP and sends an HTTP request to a remote server that was hacked by the group to serve as a malware hub, before downloading the malware. In some cases the malicious macro was password protected, but our threat actor might have forgotten that a .doc file is actually an archive and when that archive is opened in a convenient editor of your choice, the macro strings are shown in clear-text.
The malware is in plain view, modifying commonplace registry entries, such as the startup configurations, and not covering its tracks. Its binaries are not deleted in most cases, and its communication is in clear-text, where the victim can sniff the communication and grab the FTP/SMTP server’s credentials.”
The attackers control their victims using HawkEye keylogger, a commercial spying tool from HawkEyeProducts, and a configuration module containing a number of Remote Administration Tools (RATs).
According to Kaspersky Lab’s researchers, the malware actually does little to hide its presence, although it has a very serious protection from analysis: “a weak knight in a heavy armor”, Securelist says.
While it is strange on its own, most likely it indicates that only a part of the malware has been written from scratch, the rest could have been acquired somewhere else.
But regardless, the threat shouldn’t be underestimated: a keylogger discovered in just one of the command-and-control servers was able to steal 2887 Passwords, 1053 Emails and 3023 Usernames from 4928 different hosts, internally and externally, including Outlook, Facebook, Skype, Google mail, Pinterest, Yahoo, LinkedIn and Twitter, as well as bank accounts and others.
Recommendations for businesses to protect themselves:
- Сheck this location C:Users<PC-NAME>AppDataRoamingMicrosoft, if it contains executable files, you might be infected with the malware. This is a warning you should not ignore.
- The Windows System Configurations should not contain a grabit1.exe in the startup table. Run “msconfig” and ensure that it is clean from grabit1.exe records.
- Don’t open attachments and links from people you don’t know. If you can’t open it, don’t forward it to others – call for the support of an IT-administrator.
- Use an advanced, up to date anti-malware solution, and always follow the AV task list for suspicious processes.
Probably disabling macros by default isn’t the worst idea either.
Picking smaller targets
Cyber-espionage is actually regarded as a threat for high-profile entities – large corporations, enterprises, government organizations, etc. Cyber-espionage isn’t your common malware attack that often only requires an attacker to know where to get a proper piece of code.
Spying and not getting intercepted and bashed off requires a lot of technical prowess, so it’s not something that script-kiddies go for eagerly. The known spying campaigns are usually comprised of rather advanced tools, mostly custom-built, and the actors behind them are clearly motivated by getting something specific, even if the lists of their apparent points of interest are very large, as was the case with Crouching Yeti APT campaign.
However, attackers of all kinds are switching to softer targets, and cyberspies aren’t an exclusion here. There are reasons for that.
Reason 1. Mainstay and satellites
It is not a vacuum that the large enterprises are operating in: every such mainstay is surrounded by a constellation of smaller contractors and suppliers. And it is logical to assume that they may have at least some of the information the hackers are looking for.
Reason 2. Softer targets
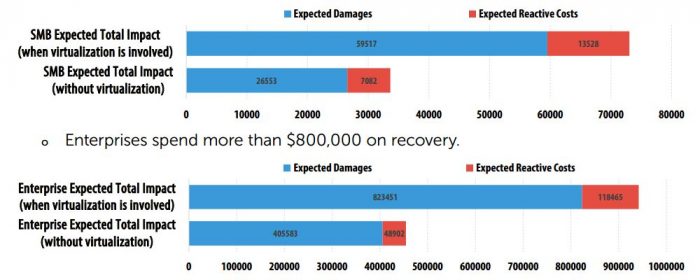
An enterprise working with some information that is of special interest for cyberspies are usually well protected and hard to infiltrate. Its satellites may be much softer targets, more brittle nuts to crack.
Reason 1+2. They may know something
Given all this, attackers may either use the “satellites” as leverage to eventually infiltrate the networks of the primary target – a large enterprise – or to “gather a full mosaic” from the accessible bits and pieces without an actual intrusion into the mainstay’s networks.
And if there is an option to extract the data of interest from the “softer targets,” hackers will definitely use it – especially when there are cybermercenaries at play: as businessmen, they are extremely interested in optimizing their effort-to-result rate.
#SMB-targeting campaigns were predicted long ago. #Protectmybiz
Tweet
In this particular case it does look like there have been mercenaries at work: the SMBs attacked by the Grabit malware operate in such diverse sectors as chemicals, nanotechnology, education, agriculture, media, construction, and more.
Probably (mind that it is mere speculation for now) this is a wide dragnet sort of intelligence-gathering operation. What is not a speculation is that it is still active and may soon expand well beyond its current geographical limits.
So it is recommended that you stay aware and ready.
 cyberespionage
cyberespionage
 Tips
Tips