Domain fronting — a technique used to shield oneself behind a third-party domain — came into the spotlight after Telegram used it to avoid being blocked by the Russian Internet regulator Roskomnadzor. This time, SANS Institute speakers at the RSA 2019 conference covered the topic. For attackers, the scheme is not an attack vector so much as a way to control an infected computer and exfiltrate stolen data. Ed Skoudis, whose report we already covered, described an action plan typical of cybercriminals seeking to “disappear in clouds.”
Most complex APT attacks are detected when exchanging information with the command server. Sudden exchanges between a computer from inside a corporate network with an unknown external machine are a wakeup call, certain to trigger a response from the IS team — which is exactly why cybercriminals are dead set on concealing these communications. It’s become increasingly common to use various content delivery networks (CDNs) for that.
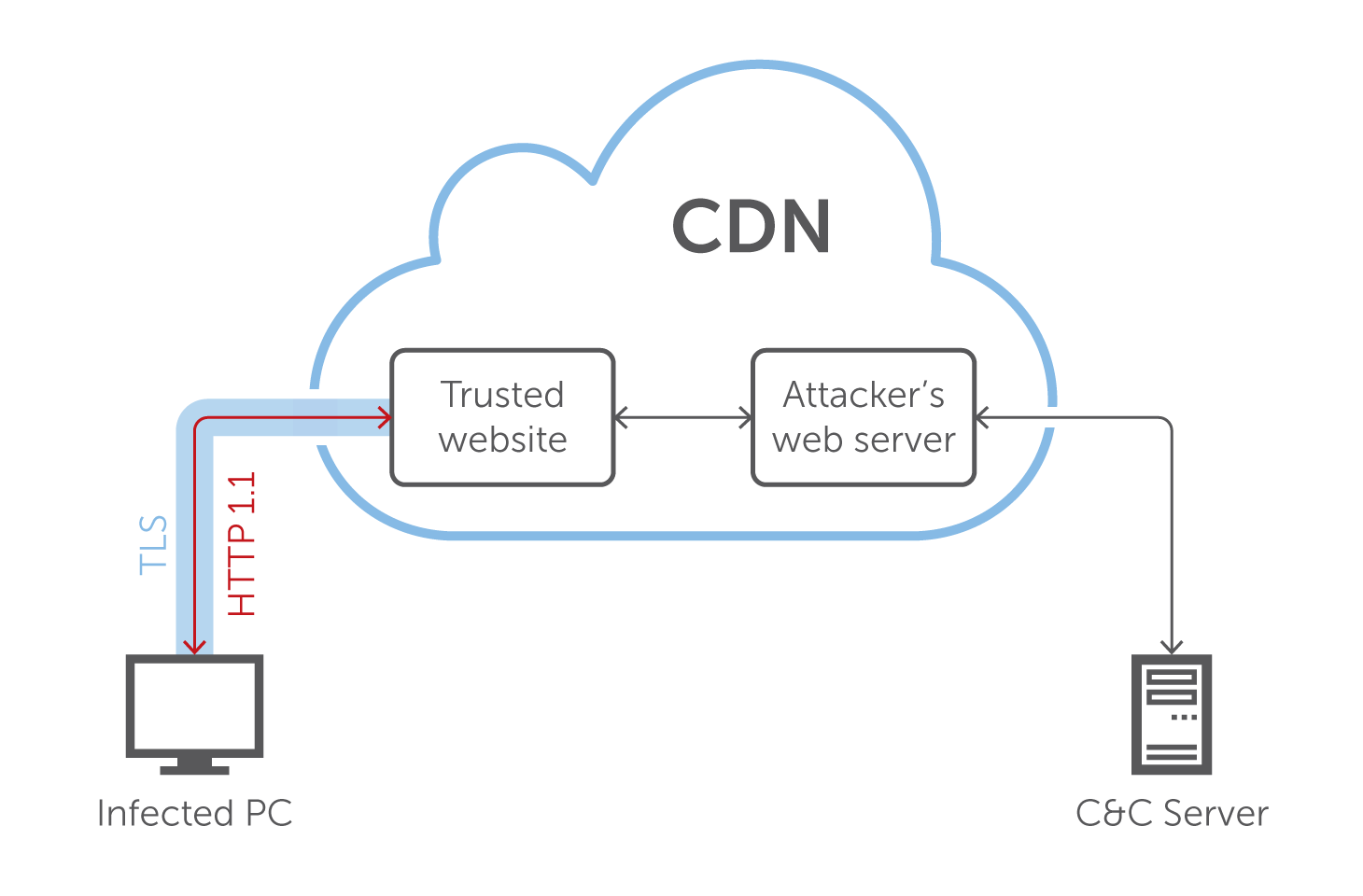
The algorithm Skoudis described looks like this:
- There is a malware-infected computer on the corporate network.
- This machine sends a DNS query to a clean and trusted website from a trusted CDN.
- The attacker, also a client of the same CDN, hosts its website there.
- The infected computer establishes an encrypted TLS connection with the trusted website.
- Inside this connection, the malware forms an HTTP 1.1 query addressing the attacker’s Web server on the same CDN.
- The website forwards the query to its malware servers.
- The communication channel is established.
To the IS specialists in charge of the corporate network, it all appears as communication with a safe website from a known CDN via an encrypted channel because they treat the CDN, the client of which is their company, as part of the trusted network. That’s a big mistake.
According to Skoudis, these are symptoms of an extremely dangerous trend. Domain fronting is unpleasant but manageable. The dangerous part is that criminals are already venturing into cloud technologies. In theory, they can create chains of CDNs and safely conceal their activities behind cloud services, thus arranging for “connection laundering.” The chances of one CDN blocking another for security purposes tend toward zero — it would almost certainly harm their business.
To deal with tricks of this sort, Skoudis recommends using TLS interception techniques. But the most important thing to realize is that it can happen and keep this cloud attack vector in mind when threat modeling.
Kaspersky Lab experts, too, have experience with such malicious tricks. Our Threat Management and Defense solution can detect such communication channels and highlight possible malicious activity.
 RSA conference
RSA conference

 Tips
Tips