Given the opportunity to decouple our clutter from the physical world, we have allowed it to spread to computers and networking resources and even as far as cloud services. Recently, online polling agency OnePoll did research comparing attitudes toward maintaining order in refrigerators versus keeping order in digital resources at work. Or rather, OnePoll’s research compared the levels of disorder.
I don’t know why they chose a refrigerator — probably because the inside of a fridge is concealed from view just like the clutter that reigns in the digital space — but I read the report with great interest, learning, for example, that more than one-third of respondents had stumbled onto their colleagues’ confidential data at work. And another third were still able to access files from their previous employers. These discoveries prompted me to recall three real-world cases from my own experience. They do well illustrating the danger of digital clutter, so I decided to share them here.
1. The remote workstation
A few years ago, I worked for a small system-integration company, where one of my tasks was writing about the company’s prerelease software products. To spare my workstation the unnecessary load of repeated program installation and removal cycles, I asked for a virtual machine. A virtual machine is easily reset to a clean system state. Using a virtual machine also appears to be a reasonable security measure — if it’s well-configured, of course.
My request was fulfilled — in part. The company did provide a VM, but only one for the whole team to share. Worse, it was connected to the corporate network; we occasionally had to share screenshots. But that is not the actual problem.
The problem is that I left the company more than five years ago, but the virtual machine is still up and running. It is still available at the same address, and it admits users with the same login and password as before. Being security-minded — more so than the company’s IT department, apparently — I signed in. I was able to see the files people were working on, and of course I immediately fired off a recommendation, which I sent to a shared printer inside the company: Change the VM password! And while you’re at it, also isolate the virtual machine from the corporate network!
2. Orphaned Google docs
Some time ago, as a freelance author, I worked with a company that was seriously concerned about its physical security. To gain admission, I had to notify one of its staffers, who would leave an admittance slip with my passport data (passports are the main form of ID in Russia) at the front desk.
At some point, I had my passport replaced with a new one. I messaged the editor about it, suggesting I could dictate the new passport data, to which he responded, “No time, do it yourself,” and gave me a link to a Google document with a list of their authors, complete with dates of birth and passport data. I tried to convey my thoughts about the matter to the man, but he was still too busy.
The problem is, the file is still there. It is still available to anyone who has that link. No one can delete any information from it, so anyone can view the editing history and see every change made to the file. The account owner cannot do anything about it, either, having long since forgotten his password and changed his e-mail address.
3. The old hard drive
I have a little hobby of collecting old computer hardware. I usually buy it for peanuts at flea markets. Not long ago, I purchased an case of old system remnants. The seller said it was trash his neighbor had told him to dump if nobody wanted it.
By way of a functional test, I booted up from the HDD just to see what it had on it. Apart from the owner’s personal stuff, there was a folder named “work” containing scores of “price quotes” and “contracts,” all marked “confidential.” The latest ones were dated August 2018.
I don’t know whether the previous owner used the old PC to work from home or just to store his archive, but he certainly had no regard for the consequences of giving it away. I formatted the HDD, of course.
I didn’t get to rummage through the refrigerators once owned by these individuals and companies, of course, but, judging by the aforementioned report, I would be certain to find horrors like year-old soup or fossilized crab sticks. It gives me the creeps just to think of the confidential data populating long-abandoned Google docs and HDDs, as well as the former employees enjoying access to corporate resources. And, unfortunately, this report supports those concerns.
 DC2019
DC2019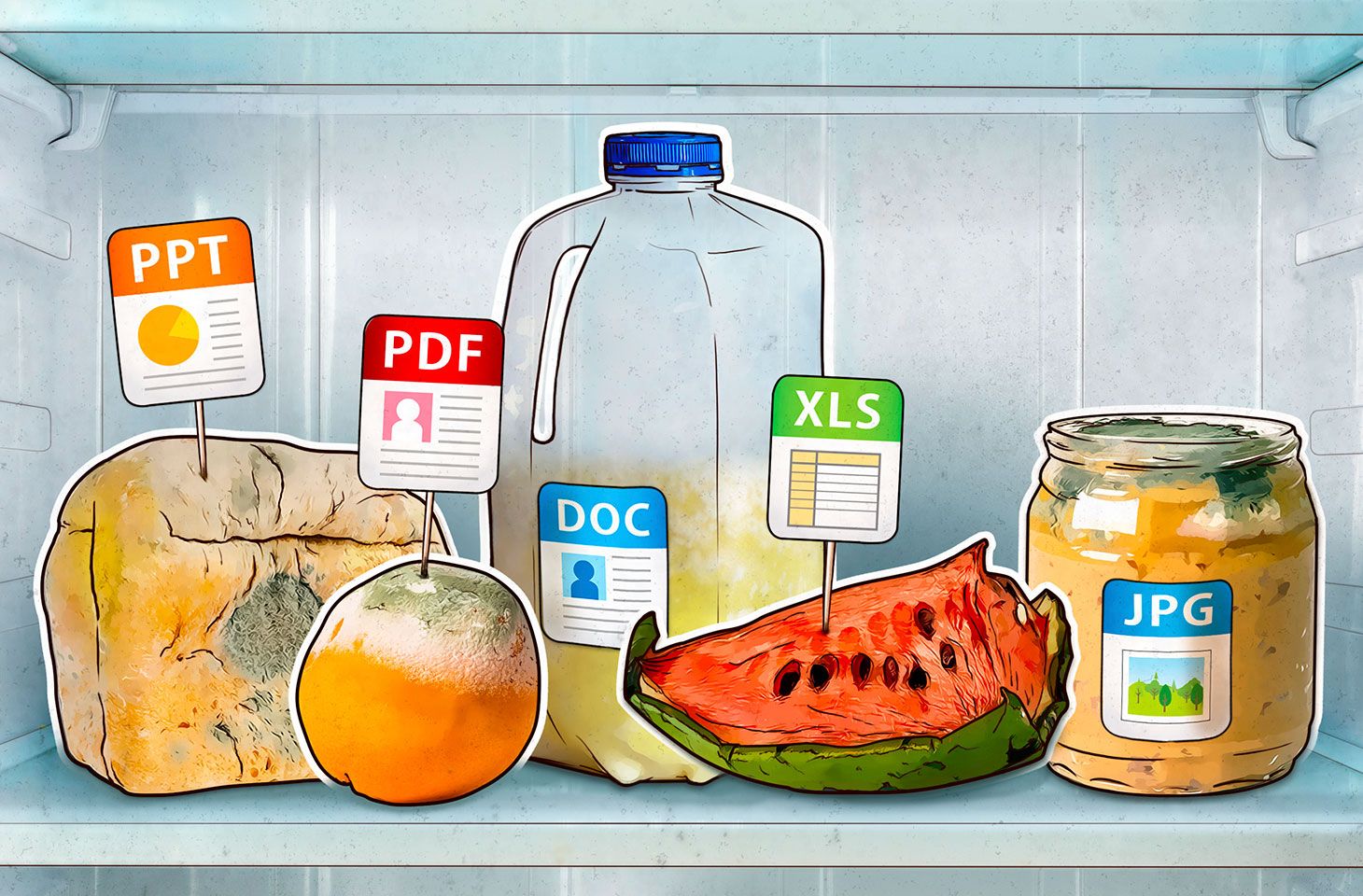

 Tips
Tips