Kaspersky Lab, together with B2B International, has conducted a new survey of IT security risks. This one was representative of 5,500 companies, both large and small, in 26 countries around the world. The focus of the survey was the overall cost of security breaches, however there are quite a few other interesting findings.
Key findings
Roughly 90% of businesses admitted they experienced a security incident over the period of survey. Incidents varied by nature – from malware incidents to a narrowly targeted intrusion – as well as by consequences. Still, 46% lost sensitive data due to an internal or external security threat.
Recovery costs for a single breach are, on average, $551,000 for enterprises and going up to $1.4 million. SMBs lose $38,000 per breach, on average.
Aside from the direct costs, there are also indirect recovery costs, adding $69,000/$8,000, respectively.
The survey is especially interesting since businesses aren’t too willing to share the information about breaches unless they are required by law to do so, or the news slips out. According to the survey’s results, just one in five cyberincidents becomes public.
Third party mishaps
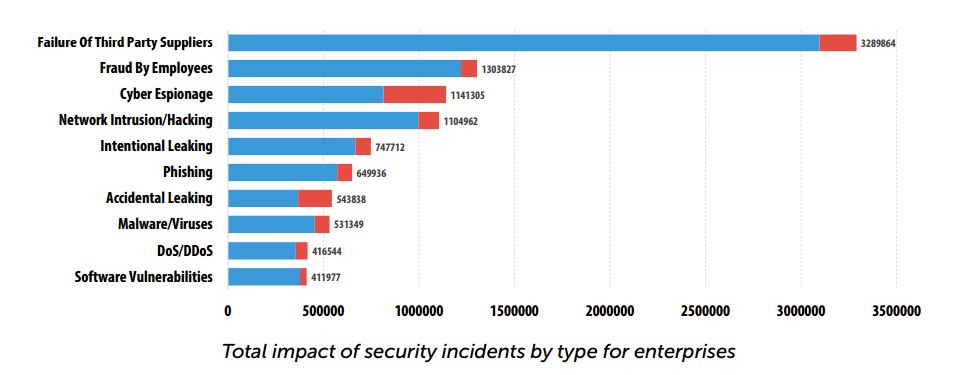
Interestingly, the survey also found that for the enterprises the most “expensive” type of incidents were “Failure of Third Party Suppliers”; “Fraud by Employees” and “Cyber Espionage” were named second and third, respectively.
For SMBs, the most costly problem reported is, surprisingly, “Cyber Espionage”; “Failure of Third Party Suppliers” has second place, “Network Intrusion/Hacking” are at third place.
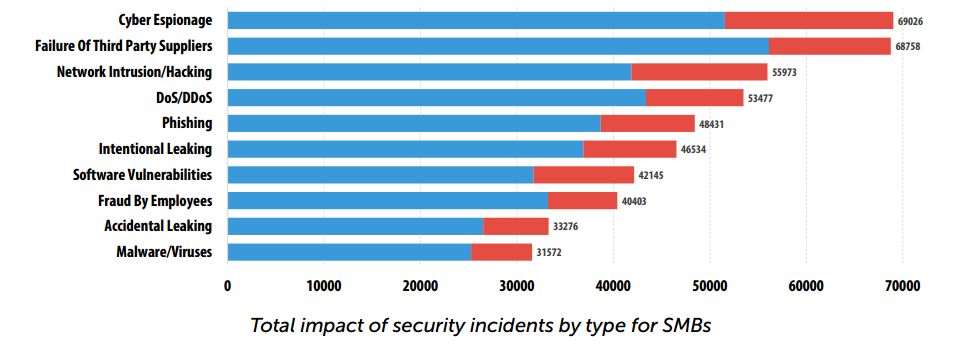
In both cases “Malware” sits low. However, surveyed businesses also said that malware was the reason for the most incidents that had caused severe security breaches.
This can easily be explained by the fact that targeted attacks and direct intrusions aren’t exactly commonplace, unlike malware attacks. Altogether, malware incidents cost businesses reasonably large sums, even if a single targeted attack is able to lose a company more than a dozen indiscreet malware mishaps.
Spending to recover
As said earlier, there are direct and indirect recovery expenses. Direct damages is money businesses have to allocate to pay for professional services to cover lost contracts and downtime.
Not all security breaches lead to downtime, but if this does occur (in about a third of incidents it does), it becomes the most expensive consequence of an attack: up to $1.4 million for large businesses.
It appears that almost all businesses, regardless of their size, have to invite external experts to recover from a security breach. Those are both technical professionals and, for example, PR experts who help to smooth out the rough edges with external communications. According to the accumulated stats, roughly 24% of companies hire PR consultants as the consequence of a security breach – which means that the breach data leaked to the public.
Additionally, Kaspersky Lab and B2B International have estimated the financial cost of damage to brand reputation:
“The value of a brand and corresponding damage are very hard to calculate, but we decided to give it a shot. We have combined consultancy expenses, lost opportunities due to damaged corporate image and spend on marketing and PR activities aimed at reducing the impact to reputation. The average losses for this particular type of damage are $8,653 for SMBs and $204,750 for enteprises”, the survey authors said.
After a security breach, most businesses try to prevent such incidents from happening in the future. This too requires extra budget, although this cannot be directly attributed to
a security breach recovery – hence the “indirect” losses. Indirect losses are the budget businesses have to allocate for additional staff hiring and training, infrastructure upgrades, etc. 75% of security breaches led to these unexpected expenses.
Awareness grows
One good news from the survey: Awareness has risen over the last 12 months. 50% of IT professionals list prevention of security breaches as one of their three major concerns. Last year, security breaches were named among the top three concerns by only 30% of respondents.
The possible reason is abundance of security breaches and APT announcements in the second half of 2014, so the general IT public’s attention has been drawn towards the issue. Still there’s large room for improvement.
Full text of survey is available here.
 enterprise
enterprise

 Tips
Tips