More Than Espionage
The majority of targeted attacks hitting businesses nowadays are conducted with cyberespionage in mind, harvesting precious business secrets or confidential personal data. But from time to time attackers get up to something completely different – like sabotage. This mode of attack is especially alarming because IT departments tend to focus on data loss/leaks, leaving them unprepared for the cyberattack-induced disruption of their whole business process, involving many different systems. Sometimes even physical consequences can result – particularly if the targeted business makes extensive use of ICS/SCADA which can be reached (a dangerous design flaw!) through general purpose networks.
Damage Incorporated
The BlackEnergy targeted attack group is a threat actor with a taste for destruction. The group has been around for some time, making a name for itself in the late 2000s with extensive DDoS attacks conducted using its namesake Trojan. Since 2014, it has attracted special attention by showing an interest in ICS/SCADA users and producers worldwide. The group’s tools and operations demonstrate their considerable skills, well above those of the average DDoS botnet masters, as well as their cyberespionage and sabotage performance capabilities.
Ukrainian companies have long been among their preferred targets; particularly ICS/SCADA companies, energy suppliers, and also the media. As though deliberately working against the tide; rather than favoring Java and Adobe Flash exploits like most of today’s attackers, the attackers prefer to deliver their infections into the confines of the targets’ defensive perimeter using Microsoft Office files.
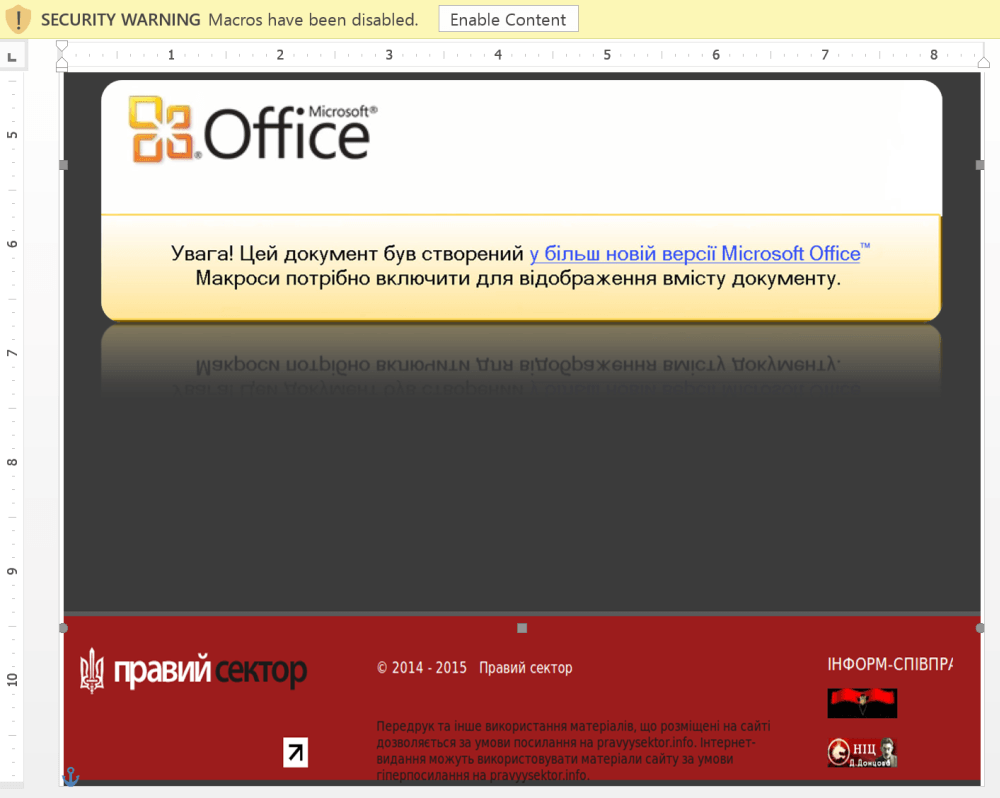
A typical specimen of their .docx lure, for example, referred to a popular news topic – the ‘Pravii Sektor’ (the Right Sector) political party – and appeared to be targeting a specific TV/media company.
The file contained an embedded macro, which puts together and runs a typical BlackEnergy dropper. To successfully execute this script in the files, the macros execution in MS Word must be enabled. So once the file was clicked on, a Microsoft Word dialogue prompted the user to enable macros in order to open it. This, the dialog stated, was because the file had been created using a later version of MS Office. This makes for a particularly successful lure in geographic regions where adoption rates for the latest software versions are low.
After successful execution, the dropper would unpack the final payload, which was launched and set for autorun.
At this stage, after receiving commands from the Command & Control server, the main module, serving mostly as a downloader, would start downloading the appropriate auxiliary modules, capable of searching and syphoning off data and/or wreaking havoc within the target’s infrastructure.
One of BlackEnergy’s most popular methods of inflicting damage is extensive data wiping. For this, they have added to their arsenal a new wiper – much more advanced than their previous disk level model – which can selectively wipe different types of data without needing administrative privileges.
Say ‘No’ to Destruction!
The malware used by BlackEnergy seems particularly well-tested against their targets’ security systems, so their operations have a relatively high success rate. Hence the necessity to be especially thorough yourself when building – or adjusting – your IT security Strategy.
Clearly, employing a standard anti-malware solution is not enough. To significantly reduce the risk of serious damage to your business, you must implement a multi-layered system. The well-known Mitigation Strategies Rankings issued by the Australian Signal Directorate (ASD) specifically state that a complex approach is needed. Such an approach would combine administrative, OS and network-based measures – as well as specialized technological measures addressing individual layers of your IT infrastructure.
And, of course, with a serious adversary like BlackEnergy, you need to leverage leading-edge technologies backed by proven Security Intelligence. Kaspersky Lab’s portfolio of solutions helps implement 19 of the 35 Mitigation Strategies suggested by the ASD. And the majority of these can be covered by one feature-rich product – Kaspersky Endpoint Security for Business Advanced.
This security platform provides not only a web of pioneering detection technologies – but also additional security layers, including Security Controls and Vulnerability Assessment/Patch Management. Application Control features, powered by our cloud-based dynamic allowlists and supporting a Default Deny scenario, are particularly applicable to the industrial sector, preventing the launch of untrusted applications (including malware) while leaving the working environment unchanged. Such controls are listed, along with Vulnerability/Patch Management, as among the Top 4 Mitigation Strategies responsible for prevention of 85% of Incidents connected with Targeted Attacks.
Given the BlackEnergy’s habit of using email-based spear-phishing, deployment of Kaspersky Security for Mail Server would create an additional powerful barrier to infection. And educating your staff, through Kaspersky Cybersecurity Awareness training, not to open every interesting-looking document they receive, can protect against a vast number of threats, as well as those posed by those committed destructors.
While the attackers may be inventive and highly experienced, planning your IT security Strategy proactively can clearly give you the upper hand against them – with the help of ever-inventive cybersecurity pioneers: Kaspersky Lab.
If you want to know more about BlackEnergy, read this article on SecureList!
Kaspersky Lab’s products detect BlackEnergy components under the following verdicts:
- Backdoor.Win32.Blakken
- Backdoor.Win64.Blakken
- Backdoor.Win32.Fonten
- Heur:Trojan.Win32.Generic
 application control
application control

 Tips
Tips